What is Server Hosting?
An independent dedicated server built to the customer's desired specifications and environment, allowing exclusive use of server resources with full root administrator access.
Our server hosting goes beyond simply providing servers and networks — we include essential services such as firewall, web DNS, web mail, network usage monitoring, and technical support as standard, maximizing value for our customers.
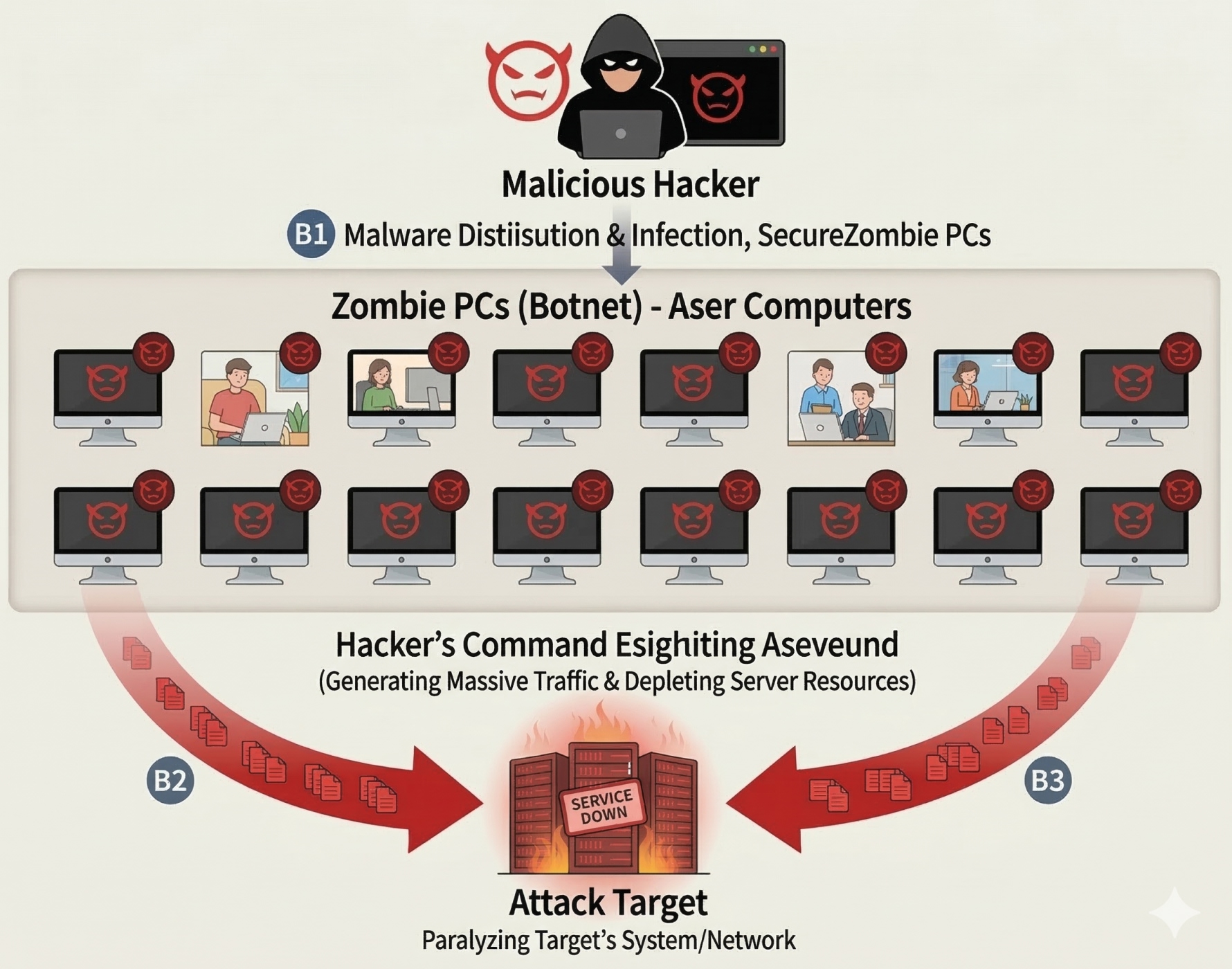
What is a DDoS (Distributed Denial of Service) Attack?
A DDoS attack occurs when a malicious hacker infects multiple computers (zombie PCs) with malware, then uses them to flood a specific site or IP with massive traffic or exhaust server resources, paralyzing the target's system or network.
This type of attack is dangerous because the simultaneous assault from infected computers makes defense extremely difficult. While past targets included adult sites, chat services, gaming, and stock trading platforms, today attacks are launched indiscriminately against any website.
Even if a hacker's demands are met, there is no guarantee the attack will stop. The best defense is to have a protective solution in place before an attack occurs.
DDoS Attack Types
| IP FLOODING | An attack that exploits the ease of reducing packet sizes compared to TCP, sending unlimited IP protocol packets to degrade network equipment performance. |
|---|---|
| TCP Attacks | - SYN Flood: Sends excessive SYN connection requests to the service port, causing service disruptions. - FIN Flood: Continuously generates and immediately terminates TCP connections to destabilize the service. - Fragment Flood: Requests fragment IP packets exceeding allowed thresholds. - GET FLOODING: Repeatedly accesses large images or specific pages to overload the DB or service. - String Attack: Embeds specific strings in packet headers targeting service daemon ports to paralyze the service. - Abnormal User-Agent: Sends packets with Agent values not typical of standard browsers to attack the server. - CC ATTACK: Continuously requests cached page information to overload the server. - TimeOut Connection: Establishes a connection state without making any subsequent service requests. |
| UDP Attacks | - Targets network segments likely to serve as a GATEWAY to paralyze the network. - Blocks external access to the gateway from unauthorized IP addresses. - Sends large volumes of UDP protocol packets to paralyze the network. |
| ICMP Attacks | - Sends large volumes of ICMP protocol packets to paralyze the network. |
NoDDoS Defense Service Architecture
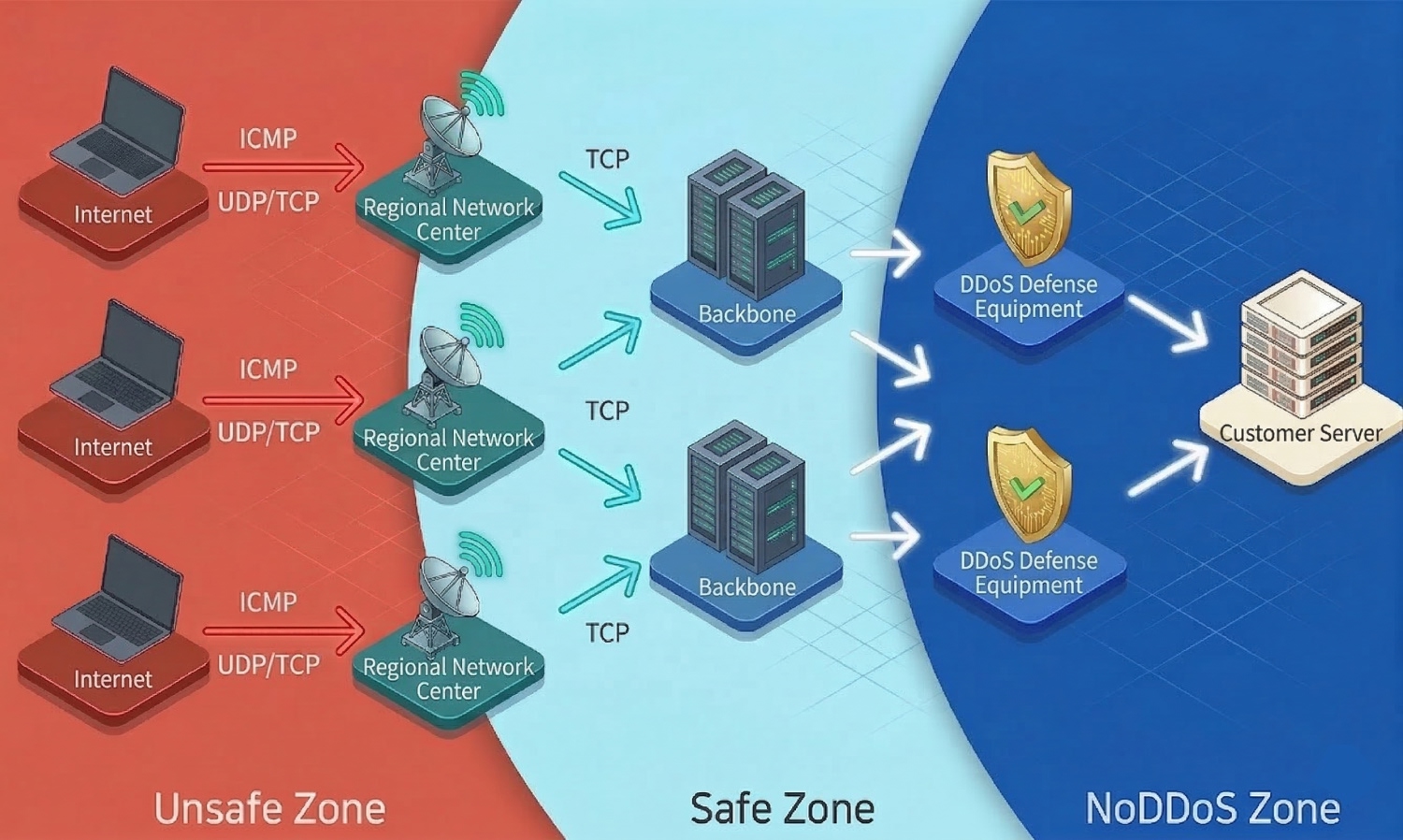
Our triple-layer DDoS security zone blocks harmful UDP and ICMP traffic at regional network centers (Layer 1), performs TCP defense at the backbone (Layer 2), and stops web load attacks such as GET Flood and CC Attack using eight 10G-class DDoS dedicated appliances (Layer 3).
When a DDoS attack is detected, real-time monitoring and alerts activate immediately, and the dedicated appliances block the attack instantly — ensuring only legitimate traffic reaches your server, with uninterrupted service 24/7, 365 days a year.
NoDDoS Defense Service Features
Capable of defending against DDoS attacks over 100G, blocking UDP Flood, and protecting against excessive ICMP attacks.
Applies defense rulesets for large-scale attacks including New TCP, SYN, ACK, Non IPS, Row IPS, HTTP Get, and CC, with session and connection attack protection.
As network bandwidth expands from 1G to 10G across institutions and major sites, handling modern networks with legacy 1G equipment brings significant cost and management challenges. NoDDoS has developed 10G-class security equipment to provide an enhanced UTM solution.
Some DDoS defense providers outsource equipment management to third parties.
NoDDoS directly owns its defense equipment and manages operations through dedicated professional engineers, enabling faster and more accurate responses when attacks occur.
Using real-time monitoring to analyze and block DDoS attack packets, rapidly respond to new attack patterns, and build a connection session defense system that limits excessive session connections per port and host to block IPs.
DDoS Defense Service Comparison
| Category | NoDDoS | Competitors (Premium) |
|---|---|---|
| 1st Defense | Unlimited Defense(160G Multi UDP,ICMP) | Null routing above 60G (UDP,ICMP) |
| 2nd Defense | 80G Cluster Defense(Individual IP & Port) | 10G Shared (TCP, Others) |
| Attack Impact | None(Auto-defense / Multi-pattern) | May be affected by other customers' attacks |
| Contract Period | No Contract — Monthly Prepaid | 3 Months / Mandatory Prepayment |
| Setup Fee | Free | 300,000 KRW / One-time |
| Billing Basis | Per Server CoreUnlimited domains and ports | 1 server, 1 domain |
 KOR
KOR ENG
ENG CHN
CHN